Cyberattacks could cost businesses $10.5 trillion by 2025, a staggering figure that underscores the critical need for robust security measures. When you outsource IT operations, you amplify these risks by expanding your attack surface and introducing third-party vulnerabilities into your technology ecosystem. This article equips IT executives with actionable frameworks and proven strategies to mitigate cybersecurity risks in outsourcing partnerships. You will learn how to implement vendor risk management, adopt zero trust architecture, enforce compliance, and maintain operational continuity while leveraging external IT expertise.
Table of Contents
- The Cybersecurity Risks Of IT Outsourcing: Understanding The Hidden Threats
- Core Cybersecurity Strategies For Mitigating Risks In IT Outsourcing
- Advanced Frameworks And Emerging Trends: Zero Trust And Continuous Monitoring In 2026
- Practical Steps To Enforce Cybersecurity And Maintain Compliance With Outsourced IT Providers
- Enhance Your IT Outsourcing Security With DevPulse
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Expanded attack surfaces | Outsourcing IT broadens your cybersecurity exposure through vendor interdependencies and supply chain vulnerabilities |
| Vendor risk management | Continuous monitoring and robust oversight reduce third-party related breaches by 35% |
| Zero trust adoption | Mature zero trust implementations cut breaches by 50% and reduce incident costs by 43% |
| Legal compliance safeguards | Rigorous adherence to GDPR, CCPA, and encryption standards protects against fines and reputational damage |
| Operational continuity planning | Fallback strategies and exit plans ensure business resilience during vendor compromises |
The cybersecurity risks of IT outsourcing: Understanding the hidden threats
When you outsource IT services, you introduce vulnerabilities that extend far beyond your direct control. Every vendor connection creates a potential entry point for attackers, expanding your attack surface exponentially. This systemic fragility means that a breach at one vendor can cascade across multiple organizations, creating widespread damage.
Consider the SolarWinds incident, where attackers compromised a trusted software provider and infiltrated thousands of organizations through routine updates. Similarly, hackers exploited a MOVEit vulnerability, ultimately compromising 66.4 million individuals’ data across numerous companies. These incidents reveal how vendor interdependencies create single points of failure that threaten entire business ecosystems.
Outsourcing decisions often prioritize cost savings and operational efficiency over embedded security frameworks. This creates dangerous gaps in access controls, monitoring capabilities, and incident response coordination. When you delegate critical IT functions, you must also transfer appropriate security oversight, yet many organizations fail to establish adequate governance structures.
The operational risks manifest in several critical areas:
- Weak authentication mechanisms allow unauthorized access to sensitive systems
- Insufficient network segmentation enables lateral movement after initial compromise
- Poor egress monitoring fails to detect data exfiltration attempts
- Inadequate patch management leaves known vulnerabilities exposed
- Limited visibility into vendor security practices obscures emerging threats
“The challenge with outsourcing is not just managing your own security posture, but ensuring every partner in your supply chain maintains equivalent standards and responds effectively to evolving threats.”
These vulnerabilities are not theoretical. Real-world breaches have exposed hundreds of millions of records, caused operational shutdowns, and resulted in massive financial losses. The cybersecurity challenges with outsourcing require proactive measures that go beyond traditional perimeter defenses.
You need to recognize that outsourcing creates a trust relationship where your security is only as strong as your weakest vendor. Without rigorous vetting, continuous monitoring, and enforceable contractual obligations, you expose your organization to preventable breaches that can devastate your business continuity and reputation.
Core cybersecurity strategies for mitigating risks in IT outsourcing
Protecting your organization requires implementing proven strategies that address vendor-related vulnerabilities systematically. These approaches combine technical controls, contractual safeguards, and operational oversight to create defense in depth.
Start with comprehensive vendor risk management that extends beyond initial due diligence. Vendor risk management programs reduce security breaches related to third parties by 35%, making continuous oversight essential. Establish formal processes for evaluating vendor security posture before engagement and maintain ongoing monitoring throughout the relationship.
Implement these critical security controls:
- Enforce multi-factor authentication for all vendor access points to your systems
- Require regular penetration testing and vulnerability assessments to identify weaknesses proactively
- Establish network segmentation that isolates vendor access to only necessary resources
- Deploy behavioral analytics to detect anomalous activity patterns
- Mandate incident response coordination procedures with defined escalation paths
- Implement data loss prevention tools that monitor and restrict sensitive information transfers
Your contracts must explicitly define cybersecurity requirements with measurable outcomes. Include specific clauses covering data encryption standards, access control protocols, audit rights, breach notification timelines, and liability provisions. These legal protections ensure you can enforce security standards and hold vendors accountable for failures.
Data encryption represents a fundamental safeguard. Require encryption for data both in transit and at rest, using industry-standard algorithms and key management practices. This protects information even if attackers compromise vendor systems or intercept network traffic.
Applying zero trust principles transforms your security model from implicit trust to continuous verification. Every access request, regardless of source, must be authenticated, authorized, and encrypted. This approach stops lateral movement and contains breaches before they spread across your infrastructure.

Develop comprehensive exit strategies for critical outsourced processes. Document how you will transition services, recover data, and maintain operations if a vendor relationship terminates unexpectedly. These fallback plans prevent vendor lock-in and ensure business continuity during security incidents.
Pro Tip: Embed security key performance indicators and audit rights directly into vendor agreements, establishing quarterly security reviews and real-time access to monitoring dashboards for ongoing oversight.
Integrating best cybersecurity practices in outsourcing requires balancing operational efficiency with security rigor. Prioritize vendors who demonstrate mature security programs, maintain relevant certifications, and provide transparent reporting. Your outsourcing security compliance contracts should reflect the sensitivity of data and criticality of services being delivered.
Advanced frameworks and emerging trends: Zero trust and continuous monitoring in 2026
Zero trust architecture represents the most significant evolution in enterprise security, fundamentally changing how organizations approach outsourcing relationships. This model operates on the principle of “never trust, always verify,” eliminating implicit trust based on network location or previous authentication.
Organizations with mature zero trust implementations experience 50% fewer breaches and reduce breach costs by 43%. These dramatic improvements stem from continuous verification, least-privilege access, and micro-segmentation that limit attacker movement. By the end of 2026, 10% of large enterprises will have mature zero trust programs in place, signaling mainstream adoption.
| Security Approach | Trust Model | Access Control | Breach Impact |
|---|---|---|---|
| Traditional Perimeter | Implicit trust inside network | Broad access after authentication | Lateral movement enables widespread compromise |
| Zero Trust Architecture | Continuous verification required | Least-privilege, context-aware | Breaches contained to minimal resources |
The shift from perimeter-based security to zero trust fundamentally changes vendor management. Instead of granting vendors broad network access, you enforce granular controls that verify identity, device health, and context for every transaction. This dramatically reduces the risk that a compromised vendor account becomes a gateway to your entire infrastructure.
Continuous security monitoring complements zero trust by providing real-time visibility into threats. Annual compliance audits no longer suffice in today’s threat landscape. You need automated tools that analyze logs, detect anomalies, and correlate events across your entire technology ecosystem, including vendor systems.
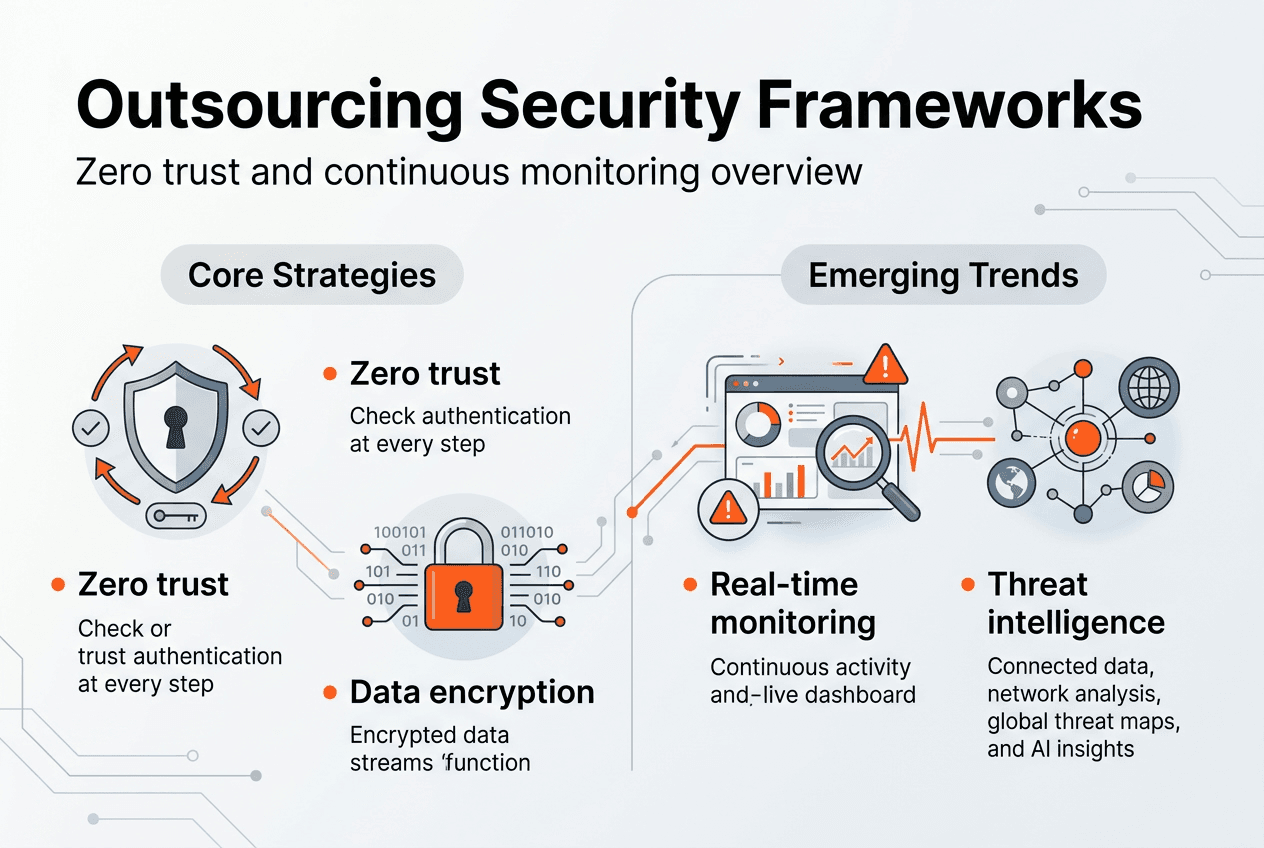
Real-time threat intelligence enhances your ability to respond to emerging risks. By integrating feeds from security vendors, industry groups, and government agencies, you can identify indicators of compromise before they impact your operations. This proactive approach enables you to patch vulnerabilities, block malicious domains, and update access controls based on current threat activity.
Implementing these advanced frameworks requires strategic planning and phased deployment. Start by identifying your most sensitive data and critical business processes. Apply zero trust controls to managed services and zero trust providers handling this information first, then expand coverage progressively.
Pro Tip: Prioritize zero trust adoption in vendors handling sensitive data to future-proof your security posture, focusing initial efforts on financial systems, customer data repositories, and intellectual property assets.
Your outsourcing security architecture should integrate these frameworks from the beginning. Design vendor access patterns around zero trust principles, establish continuous monitoring requirements in contracts, and ensure vendors can provide the telemetry needed for effective oversight. This foundation enables you to scale securely as your outsourcing relationships grow.
Practical steps to enforce cybersecurity and maintain compliance with outsourced IT providers
Enforcing cybersecurity requirements demands clear contractual language backed by operational verification. Your outsourcing agreements must explicitly define security standards, compliance obligations, and consequences for failures. Include specific clauses covering encryption requirements, access controls, incident notification timelines, audit rights, and data handling procedures.
Map your critical business processes to specific outsourcing vendors and assess the impact of potential service disruptions. This dependency analysis reveals where you need redundancy, alternative providers, or internal capabilities to maintain operations during vendor compromises. Document these fallback plans and test them regularly to ensure effectiveness.
Adopt continuous security assessments rather than relying on annual audits. Organizations with mature third-party risk management programs experience 20% fewer data breaches than less mature programs. Implement automated scanning, regular penetration tests, and ongoing compliance verification to maintain current visibility into vendor security posture.
Compliance with data privacy regulations is non-negotiable when outsourcing across borders. GDPR imposes strict requirements on data transfers outside the European Union, while CCPA governs California resident information. Ensure your vendors implement appropriate safeguards, maintain required certifications, and provide documentation demonstrating compliance.
The Conduent SafePay case illustrates the catastrophic consequences of inadequate security controls. This ransomware breach exposed 26+ million individuals’ data and caused multi-million dollar response costs. Poor egress monitoring allowed attackers to exfiltrate massive data volumes before detection, highlighting the need for comprehensive network visibility.
Implement systematic data encryption and behavioral analytics:
- Encrypt all data transfers between your systems and vendor infrastructure
- Deploy endpoint detection and response tools on systems with vendor access
- Monitor for unusual data access patterns that may indicate compromise
- Establish baseline behavior profiles for vendor accounts and alert on deviations
- Require vendors to maintain detailed access logs for forensic analysis
| Incident | Organizations Affected | Records Compromised | Estimated Cost | Root Cause |
|---|---|---|---|---|
| SolarWinds Supply Chain Attack | 18,000+ | Unknown | $100M+ | Compromised software update mechanism |
| MOVEit File Transfer Vulnerability | 2,000+ | 66.4M | $10B+ | Unpatched SQL injection flaw |
| Conduent SafePay Ransomware | 1 | 26M+ | $15M+ | Inadequate egress monitoring |
These incidents demonstrate that even sophisticated organizations face devastating breaches through vendor relationships. Your outsourcing security governance must account for these risks through layered defenses and rapid response capabilities.
Establish clear communication channels and escalation procedures for security incidents. Define who gets notified, what information must be shared, and how quickly vendors must respond. Regular tabletop exercises test these procedures and identify gaps before real incidents occur.
Your IT support and maintenance security strategy should integrate these enforcement mechanisms from day one. Build security requirements into service level agreements, establish performance metrics that include security outcomes, and conduct regular reviews to ensure ongoing compliance.
Enhance your IT outsourcing security with devPulse
Navigating the complex landscape of IT outsourcing security requires partners who understand both technical excellence and business risk management. devPulse delivers comprehensive software engineering services designed with security embedded at every layer, from initial architecture through ongoing operations.
Our specialized technical support and maintenance capabilities strengthen your security posture while ensuring operational continuity. We implement the zero trust principles, continuous monitoring frameworks, and compliance safeguards discussed throughout this article.
Explore our software development case studies showcasing successful partnerships where security and innovation drive business outcomes. Partner with devPulse to build resilient, secure technology solutions that protect your organization while enabling growth.
Frequently asked questions
What are the top cybersecurity risks when outsourcing IT services?
Access control weaknesses represent the primary risk, allowing unauthorized users to compromise vendor systems and pivot into your infrastructure. Third-party vulnerabilities create additional exposure through unpatched software, misconfigured systems, and inadequate monitoring. Supply chain attacks exploit trust relationships to deliver malware through legitimate update mechanisms. Data exfiltration risks increase when vendors lack proper egress controls and encryption.
How can I ensure my outsourcing providers comply with cybersecurity standards?
Include detailed security and compliance clauses in vendor contracts specifying required certifications, encryption standards, and access controls. Require regular penetration testing and vulnerability assessments with results shared directly with your security team. Implement continuous vendor monitoring through automated tools and establish audit rights that allow independent verification of security practices. Conduct quarterly business reviews that include security performance metrics and remediation tracking.
What benefits does implementing zero trust bring to outsourcing security?
Zero trust reduces breaches by 50% and lowers incident costs by 43% through continuous verification that eliminates implicit trust. This architecture stops lateral movement by requiring authentication for every access attempt, preventing compromised vendor accounts from spreading across your infrastructure. Mature zero trust programs enhance overall outsourcing security posture by enforcing least-privilege access and providing granular visibility into user behavior.
How often should third-party security assessments occur?
Continuous monitoring with automated tools is preferred over annual assessments, providing real-time visibility into emerging threats and configuration changes. Deploy security information and event management systems that analyze vendor activity continuously. Real-time threat intelligence improves detection of indicators of compromise before they cause damage. Assessment frequency should increase based on vendor risk profile and data sensitivity, with high-risk vendors receiving monthly reviews and critical providers undergoing weekly automated scans.